PolarProxy
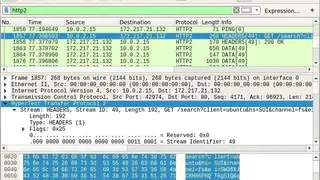
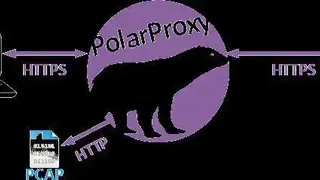
PolarProxy is an SSL and TLS proxy software designed for malware researchers and incident responders. The software primarily functioned to encrypt or decrypt TLS encrypted traffic direct from the malware. PolarProxy can re-dimension itself to re-encrypts TLS traffic, and at the same time, it can save the decrypted traffic in a PCAP file and after can be open with the help of IDS. The software can be used either individually or commercially, but there is a limitation on the sessions to be proxied per day.
Polar proxy runs with the different modes of operations, such as forward proxy, reverse, TLS termination, and transparent in-line proxy. You can use the on mode to intercept, monitor, and reverse proxy to watch TLS traffic arrival. PolarProxy elegantly terminates the TLS encryption for the incoming connections, and you can use the terminate option in releasing the TLS encryption. Finally, the in-line proxy decrypts, re-encrypts, and forward all the TLS connection to the particular proxy, security gateway, or NG firewall form.
PolarProxy Alternatives
#1 Surge for Mac
Surge for Mac is an advanced debugging proxy software that lets you meet all the network’s personalization requirements. The software is a highly powerful network tool known for its high-performance proxy servers, such as HTTP and SOCKS5. The Surge has a powerful capability to intercept and logging the network traffics summary and allows you to transfer the traffic to the other servers via configuration. There are multiple protocols for your support, like SOCK5, HTTP, TLS, SOCKS5, and HTTPs.
The software comes with a directional dashboard, which makes Surge a best-in-class sophisticated HTTP debugging tool. You can monitor all the requests over the network, redefine requests, manipulate the DNS map, and adjust all the proxy rules. There are multiple features to offer that include high stability of structure, flexible rule system, integrated with IOS version, enhanced and gateway mode, HTTPs decryption, metered network mode, and more to add. Furthermore, Surge is a platform where massive networks are handled, and certificates are delivered, connections are made, functional modules are offered, and more with the central system.
#2 Weer
Weer is a protocol HTTP debugger tool that provides you HTTP proxy to capture traffic and send a request via the proxy. The software is based on original Chrome DevTools to permit the continuous usage to debug HTTP traffic.
The software comes with the support either for forward or reverses proxy, and you have an advantage of PCAP file format for easy capturing. The software is lightweight and has an easy setup and can be run on Windows, Linux, and macOS. Moreover, you have a leverage of protocol like WebSocket and HTTP 1.1 to execute a file with less than 1MB.
#3 LightProxy
LightProxy is a cross-platform designed to perform a debugging proxy and provides full automation with certificates and system proxy settings. The software is powerful in its approach to monitor, host, and capture web traffic from your browser.
LightProxy shows good performance with its HTPP or HTTPs servers that will set things nicely to manipulate the traffic between inspection. Wildcard mapping function will set the things to solve complex claims, either the wild card matching or wildcard domain name matching. LightProxy, with its hackable approach, permits you to write your rule with node.js.
#4 James
James is an operative HTTP proxy and monitoring software that legitimates developers to view and intercept requests made directly from the browser. The software is entirely proactive in manipulating traffic and control requests over the network with ease.
The software allows you to redirect the request and URL wildcard mapping, but you can also use multiple wildcards from the same URL. James gives high performance with its proxy servers, making it one the best debugging tool for the web. Furthermore, with James, it is easy to script, inspect, pull requests, manipulate responses on traffic, and more.
#5 Live HTTP Headers (Chrome)
Live HTTP Headers is a featured rich extension for Google Chrome to logs all the HTTP traffic between your chrome browser and the internet. The software is featuring support for operational monitoring of HTTP or HTTPs traffic from your browsers. Debugging is comfortable with the Live HTTP headers to debug a web application and manipulate the traffic at level best and redefine your traffic with ease.
The software provides in-depth information to determine the technology if the page is encoding, cached, or anything else. This extension provides you all the headers sent to the servers and can be back with the response. The good thing about the Live HTTP headers that are not making a second request as other extensions commonly do. You can find multiple features such as redirect path, cookies on remote sites, HTTP verbs used, Response codes, and more.
#6 HTTP Headers
HTTP Headers is an intelligent software designed to provide information about the HTTP header for the current URL. The software helps to debug web-application, see cookies sent by the remote site, check server-return, HTTP verbs used, and responses code.
HTTP Headers show the headers if they are sent to the page and do not make a second request. As a site owner, you can quickly access the current HTTP request and responses in case of errors. HTTP Headers is useful in either sending or receiving requests from a web server, and you can accelerate the website and strengthen it against attacks.
#7 Cellist
Cellist is an all-in-one HTTP debugging proxy software designed for OS that provides a straightforward approach to put a proxy between the HTTP client and the internet. You need to set the proxy configuration on your device, and all the HTTP traffic will go through and can be revealed to you.
The software provides you support for any device such as Mac, Windows PC, mobile, and Linux to records all the HTTP. Cellist is surfacing the body viewers that makes things easy to inspect body data effortlessly. The software provides reliable charset detection of the character of the encoding of HTTP body data to avoid mojibake.
#8 HTTP Analyzer
HTTP Analyzer is a software utility to capture and monitor HTTP or HTTPS traffic in real-time. The software provides you with a wide range of information such as content, query strings, post data, request and responses, redirection URLs, cookies, post data, and much more. The software is integrated with the Internet Explorer and Firefox, which means no swathing between the windows, and you can analyze the HTTP traffic and web page in the same window.
HTTP analyzer shows you the unencrypted data over HTTPS or SSL connections having the same level of detail as in the case with HTTP. The software is dispensing a color time chart to point out the relative between a single network timing and other segments’ timing in the available request. HTTP Analyze surfaces multiple IE tamper features, detect potential problems, native support for flash reporting, request builder, automated interface, and more to add. Furthermore, the software is aimed to enhance productivity via proper examination of requests and issues.
#9 Charles
Charles is an all in one web debugging proxy software based on the HTTP debugging proxy server application written in JavaScript. The software enables its users to view HTTOP, HTTO2, and HTTP traffic, and you can easily access TCP via the local computer. Charles is making its mark with its display of data that is either received or sent. Your web browser can access the internet through Charles with the help of configuration.
The software is functional and provides you with extreme support with its quick, reliable, and advanced debugging saves your time and keeps you out from any overheads. Charles is being exceptional with its validation of recorded HTML, RSS, and CSS responses courtesy of having a W3C validator. There are multiple features on offer: breakpoint support, repeat request, AJAX debugging, bandwidth throttling, SL proxy, and more to add.
#10 Mitmproxy
Mitmproxy is a reliable and interactive HTTPS proxy software that helps test, debug, penetration testing, and privacy measurements. The software is useful for inspection, modification, intercepting, and replay web traffic like WebSockets, HTTP/2, HTTP, and other protected protocols such as SSL or TLS. Mitmproxy software features support decoding various message types ranging from HTML to ProtoBuf.
The software is extensively intercepting the messages, and before reaching the destination, they are modified and finally replay them to a server or client. Mitmproxy comes with a graphical interface with several features with mitweb that will give the same kind of experience with other applications or devices. Moreover, you have the leverage to write powerful adds-on Mitmporxy, and possibilities are also there to do a modification, redirect traffic, visualize messages, or apply custom commands automatically.
#11 Burp Suite
Burp Suite is a best-in-class application security testing software with the leading cybersecurity tools to fight against cybercrime. The software provides an automated approach throughout your journey to protect things when you are online. Burp Suite is suitable for professional use, but its high considerations on simplicity, discovering elegant reports, scheduling, and straightforward remediation advice in one flexible package.
The software is dispensing enhancements with its continuous updates on scanning logic that makes it sure to find the latest vulnerabilities. Burp is a leader in detecting novel vulnerabilities such as web caching poisoning and template injection. The software is highly recognized because of its out-of-band techniques to raise the conventional scanning model. Multiple features are asynchronously triggering, detailed custom advisories, SAST and DAST techniques, automatically handling of sessions, state, and changes, infiltrator, scan history, repeated scan, and more to add.
#12 OWASP Zed Attack Proxy (ZAP)
OWASP Zed Attack Proxy (ZAP) is a crack of a tool among all security software that comes with the server, allowing users to manipulate traffic. The software can be run in a daemon mode that is effectively controlled under rest API. Zap is automating your security journey by providing API that allows you to do everything you can from your desktop interface. The developers are delighted to have an automated approach for pen-testing and security regression testing in the CI or CD pipeline.
ZAP has something new: active and passive scanners, traditional and AJAX spiders, brute force scanner, web sockets, and port scanner. The software is doing things with a better approach via creating a proxy server and makes your website traffic pass through the designed server. Then auto scanner does the rest for intercepting the vulnerabilities on your website. Furthermore, using the Zap latest version means you can browse and download the add-ons with the right click on the toolbar.
#13 HTTP Toolkit
HTTP Toolkit is an elegant debugging, mocking, testing, and building software with HTTPS on multiple devices such as Mac, Windows, and Linux. The software comes with a reliable, functional strategy that streamlines your way of intercepting and viewing HTTP, mock servers, injecting errors, redirecting, or rewriting. HTTP Toolkit is robust to proxy any HTTP or HTTPS traffic search, and you can explore and inspect HTTP requests and responses, which is one click away for chrome, Python, Node.js, Ruby, and more.
The software features support the edit option to test APIs and clients for HTTP error simulation, timeouts, and failed connections. HTTP Toolkit is a leader to validate request performance and debugging caching, and compression is the level best that you expect from a world-class tool. When it comes to its features, many are listed: automatic setup for the targeted interception, backend, and scripting languages, examine the URL, status, and headers, precisely matched request, manually respond to the request, and much more.
#14 Proxyman
Proxyman is an advanced software for a web-debugging proxy that is a native and mountain performant macOS application that is easing the way to manipulate HTTP or HTTPs requests. The software fully-features has a nimble approach to validate submissions. Developers are delighted to have Proxyman in their tool bank to complete their tasks and professionally collaborate with the team. It is all about sophisticated proxy core, and Proxyman is just doing the same with the minimum system resource usage.
SSL proxy is giving many possibilities to generate more certificates to have an HTTPS. The software is integrated with IOs simulators and iOS, and all the debugging process have immense support with the inbuilt tool. There are multiple features on external proxying, block list, repeat request, local map, content filter, numerous tabs, scripting, and much more to add. To boot, Proxyman is valuable to lift your battery life while maintaining your internet connection’s stability at the same time.
#15 CacheGuard OS
CacheGuard OS is an intelligent appliance-oriented operating system that is powerful and easy to handle for Web Gateway appliance. The system is mainly designed for the processing of web traffic. CacheGuard OS integrates with the best-in-class technologies to have a productive solution that will surface web optimization and secure your web traffic without having the overhead of security layers. The all in one web optimization under CacheGuard OS leverages you with persistent web caching, web cache sharing, and HTTP compression.
The system paves the way for reverse proxy, guarding, web proxy, URL, SSL inspection, web caching, HTTP Compression, and bandwidth shaping via emending technologies. All the technologies combine to strengthen web security and Web traffic optimization. Multiple elegant network features are Network appliance, internet gateway, web load balancer, traffic, Shaping, NTP support, and much more. Moreover, CacheGuard is dispensing various features For IP security, web security, OS capabilities, administration.
#16 HTTP Debugger
HTTP Debugger is easy to use software for debugging HTTP API calls either between backends or to backends. The software has a transparent interface, and your network failures and short ramp-up time. The system does not change your browser’s configuration, and you have a display of proxy-connected traffic. HTTP debugger leverages you with HTTP API endpoints, isolates and fixes performance bottlenecks, and easy detection and elimination of security bugs.
You can seamlessly resubmit tweaked HTTP sessions back to your server, which provides easy tests or detection of security issues to your code. The software lets you identify and removes problematic integrations with third-party systems. You can measure the network performance of your applications with an isolated methodology. SSL decryption is easy with an HTTP debugger that permits the SSL traffic to form your browser or desktop application virtually. Furthermore, you have support to export data in various formats and can send and recreate session files.
#17 Camilla Proxy
Camilla Proxy is an all in one web debugging proxy software that has built its reputation with its high performant manipulation and by-default zero configuration requirements. The software has an easy installation setup, and it is easy to configure the Comilla Proxy to your server. Comilla Proxy is particularly useful in finding data transfer from your Web API during development and troubleshooting.
The software is sustainable for its support and designed to be up and running in your production environment. Camilla Proxy defines its location to work between your application and third-party HTTP API to which the communication is going through. Furthermore, the software is based on high performance, having a good inspection for your server-to-server HTTP communication.
#18 Proxie
Proxie is a reputable software designed for HTTP debugging that is highly responsive for seamless operations running on the go. The software comes with the snap and has an interface for smooth performance. Proxie has an automated approach to decrypt and reveal HTTPs traffic between interception. The software is known for its manipulation of requests and responses, and you can manually pause and edit and imply JS scripts on them.
The software is designed for macOS, and user-experience, productivity, RAM, usage, and battery life are Porxie’s main priorities. Porxie is dispensing a comprehensive filtering system for the convenient multiple filtering mechanisms such as quick search, customizable user filters, and URL hierarchy. Map Local and Anticache are intuitive to configure for common tasks, and if you want more customizable options, you can go for Scripting rules and JavaScript.
#19 HttpFox
HttpFox is an elegantly designed add-on for Firefox that enables you to monitor HTTP traffic generated by your web browser. The software is a reliable way to control and analyze the input and output petitions from your browser directly without running a different application. You can ultimately know your data transferred or the associated URL to every petition. You can do multiple options such as automatically start watching, color the request, and remove the inhibit caching request channel flag.
It helps classify the traffic depending on the type of protocol you used, such as CSS, JavaScript, and HTML. HttpFox comes with the headers, and you can control the cookies, content, calls, and post parameters. Moreover, in a new tab, the configuration of HttpFox to run at Firefox startup permits to control the traffic like with the case in another application.
#20 HTTP Scoop
HTTP Scoop is an intelligent HTTP protocol analyzer designed for macOS that automatically captures HTTP conversations between the HTTP client and server. The software provides real-time information between the server and the client. You have the leverage of having different aspects of conversation, such as to request URL and parameters, post data, file sizes, encoding information, and request or response headers.
HTTP Scoop permits you to view the returned files in the form of text or either in image format or hex, and you save them on the disk. You can expertly analyze the cookie behavior and see how the cookie is exchanged. Regardless of the browser you are using on your Mac, HTTP Scoop will bring the right information about the HTTP request, and there is no unique configuration required. You need to click the Scoop button, and let’s begin your journey with HTTP Scoop.
#21 Uthrottle
Uthrottle is a useful tool designed for your convenience to simulate custom connection conditions and limit the traffic over the network. You have the advantage of having specified speed on the network interfaces, and you have no overheads of the bug’s manifestation.
The software is reliable to test your environment for how you can slow down your network interface speed and various other factors, including latency rate. Uthrottle is a quick way to overcome all the testing requirements, and you can test your projects with ease. Regardless of any conflict, you can perform various actions and can throttle multiple interfaces at once.