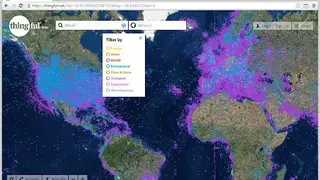
Thingful
Thingful is an IoT search engine that provides a unique geographical index of connected objects in the world. It includes weather, energy, radiation, air quality devices, ships, iBeacons, animal trackers, and even seismographs. With its powerful search abilities, you can use connected sensors, objects, datasets, and real-time data sources across many popular IoT networks. The RESTful API lets you search for IoT objects that you have the authorization to find in a specific location. You can get a snapshot of the data as well as the URL to query those devices directly.
Thingful makes it quick and easy to find and use the IoT data that’s most valuable to you, providing access to the world’s largest searchable index of public and private connected objects and sensors around the world from dozens of IoT networks and infrastructures. This allows people and companies to claim and verify ownership of their things. Additionally, you can add objects to a watch list in order to keep track of them and monitor their real-time status and get notifications when they change.
Thingful Alternatives
#1 ZoomEye
ZoomEye is one of the top global cyberspace remapping and China’s first cyberspace search engine. It allows you to continuously scan and identify various service ports and protocols 24 hours a day and map the local or whole cyberspace. It continuously accumulates a large amount of surveying and mapping data for trend analysis and dynamically mapped cyberspace across time and space. A feature called Knownsec Security Brain can record the IPs where cyber-attacks are actively launched and tag them as malicious. Therefore it allows you to identify the target more practically in order to avoid blindly attacking the target and to reduce related risks.
ZoomEye activates the resolution of IP’s geographic location, which is accurate to the building level and has an error of less than 50m, allowing you to learn more about IP information from more dimensions. ZoomEye has the powerful capability of processing online data. It can conclude accurate industry information from IP’s multi-dimensional data, deeply analyzing IP data and giving data a soul, so that IP information here is no longer a simple number
#2 Armitage
Armitage is an open-source cyber-attack management tool that visualizes the targets and warns about incoming attacks. It allows the network attack team to communicate in real-time, share the data, and easily share access to hosts compromised with the Metasploit exploitation framework. It makes it possible to import hosts and launch scans to populate Metasploit’s database with service and target information. Armitage’s UI also shows the target database in a table or graphical format. A feature called Find Attack recommends remote exploits using known host and service information. You can also launch browser exploits, create Exe files, and generate malicious files to call back Metasploit from Armitage
It has a bunch of post-production tools to escalate privileges, dump password hashes to a local credential database, browse files, and open command shells. The SOCKS proxy module turns it into a proxy server that routes ongoing connections via existing pivot points. All in all, Armitage is a great tool that you can consider among its alternatives
#3 Social-Engineer Toolkit
Social-Engineer Toolkit is an open-source Python-based tool that allows you to test penetration around social engineering. It has multiple custom attack vector that lets you make a pre-defined attack within no time. The attacks built into the toolkit are designed to be targeted and focused attacks against a person or organization used during a penetration test. By default, the SET works just fine, but mostly, advanced customization may be needed in order to ensure that the attack vectors go off without any problem.
There is a section named Ettercap that can be used when you’re on the same subnet as the victims, and you want to perform DNS poison attacks against a subset of IP addresses. When this flag is set to ON, it will poison the entire local subnet and redirect a specific site or all sites to your malicious server running. A feature called Java Applet Attack vector is the attack with one of the highest rates of success that SET has in its arsenal. To make the attack look more believable, you can turn this flag on, which will allow you to sign the Java Applet with whatever name you want.
#4 Exploit Pack
Exploit Pack is an integrated environment for executing and directing a proficient penetration test. The tool is designed to focus on what really matters by automating all the processes. You can measure threats, vulnerabilities, impact, and risks related to exact cyber-security events by rapidly reacting to the integration of both offensive and defensive security. Exploit Pack uses a progressive interface that supports rapid reconfiguration to adapt exploit codes and benefits to the constantly evolving threat environment. It lets you improve and close the circle by measuring, tracking, and reacting.
The tool lets you quickly modify, reconfigure, or add new exploits to the framework. Exploit Pack provides you with a unique set of features to assist you during the exploitation process. In short, you can replicate real-world attacks and use the network before hackers do. The pricing starts from $200 per month that includes every feature except zero-day exploits, monthly training, and support. The premium package costs $900 per month with every feature available.
#5 Cobalt Strike
Cobalt Strike is a threat emulation software designed to perform adversary simulations and red team operations. It recognizes which client-side application your target is using with every bit of information about the program. You can import a message and let Cobalt Strike replace links and text to build a convincing phish for you. A feature called Beacon is Cobalt Strike’s payload to structure an advanced actor. Beacon performs PowerShell scripts, logs keystrokes, takes screenshots, downloads files, and spawns other payloads.
You can also use a browser pivot to apply two-factor authentication and access sites as your target. Other features are lateral movement, privilege escalation, post-exploitation, pivoting, and weaponization. All in all, Cobalt Strike is a great tool that you can consider among its alternatives.
#6 Immunity CANVAS
Immunity CANVAS is an automated exploitation program with a comprehensive set of features and development frameworks available for penetration testers and security professionals. Immunity CANVAS comes with a unique beaconing feature. You can instruct the compromised host to attempt to connect to a pre-defined address at a set interval and receive a shell. This way, if new firewall rules are constructed during your pen test, there’s still a reasonable chance of maintaining connectivity. It establishes a real-world persistence inside your infrastructure and provides real-world indicators of compromise to your incident response team.
To provide maximum reliability, it always attempts to reuse the socket, and if the socket reuse is not suitable, then the connect-back is used. Additionally, you can set the split-bouncing automatically and adjust the covertness level. All in all, Immunity CANVAS is a great exploitation tool that you can consider among its alternatives.
#7 IVRE
IVRE is an open-source framework for network penetration. It gathers data from network intelligence, stores it in the database, and provides tools to analyze it. MongoDB is recommended for maximum reliability. The web interface allows you to analyze Nmap scan results, and due to the fact that it relies on a database, it can be much more efficient with huge scans than a tool like Zenmap. The easy-to-use interface lets you browse network flows with ease. It lets you import the results from Zeek, Argus, or Net flow, and the data can be explored from a CLI and Python API.
After getting the results, you can process it with your favorite analysis tools lie RT Graph and matplotlib. Additionally, you can also filter, have quick access to previous results for a specific host, and look for specific services or vulnerable versions within a specific country or network, etc. IVRE includes tools to run Nmap against targets like a network or an address range, a whole country, a specific AS, or the full IPv4 connected address space.
#8 Core Impact Pro
Core Impact Pro is a program designed to allow security teams to conduct advanced penetration tests with a comprehensive set of features. The guided automation and certified exploits of this software ensure safety tests in your environment. Its Rapid Penetration Test feature provides accessible automation, which is built to automate repetitive tasks. These high-level tests allow you to optimize your security resources by simplifying the process and focus on more complex issues. A highlighting feature of this tool is a professionally written and validated exploit library for real-world testing capabilities.
This library of commercial-grade exploits has real-time updates of new penetration testing exploits and tests for additional platforms as they become available. You can replicate attacks across network infrastructure, endpoints, web, and applications to reveal exploited vulnerabilities, empowering you to immediately remediate risks. Core Impact Pro’s patented core agents simply your interactions with remote hosts that are compromised. All in all, Core Impact Pro is a great tool for security and penetration tests.
#9 BinaryEdge
BinaryEdge is a platform that acquires internet data and transforms it into threat intelligence fees for security reports. It provides a distributed platform of scanners and honeypots to acquire, classify and correlate different types of data. It then uses all of these data points to match those digital assets to an organization, allowing us to provide a global, up-to-date view of organizations’ known and unknown assets. The premium users also get real-time search and third-party integration.
It continuously gathers and interconnects the data from the internet that allows the organization to keep an eye on what is their attack surface, and there is any loophole for attackers in the infrastructure. The considerations are databases, invalid SSL certificates, possible vulnerabilities, ports and service exposure, misconfigured network shares, etc. Its distributed network collects worldwide events across residential and enterprise providers to give clients a real-time view of what is happening on the internet.
#10 Sn1per Professional
Sn1per Professional is an attack surface management solution that lets you discover the attack surface and prioritize the risk. The attack surface can be IPs, domain names, HTTP headers, open ports, etc. With its IT asset inventory, you can search, sort, and filter for IP titles, DNS, server headers, and open ports of whole attack surface inventory. The vulnerability management lets you quickly scan for the latest vulnerabilities using its proprietary scanners. Besides that, you can also schedule scans on a daily or weekly basis from continuous changes and coverage.
Sn1per Professional can automate the threats discovery and ethical exploitation by using its latest hacking security tools. The workspace navigator is there to help you in sorting, managing, and searching all your workspaces without wasting any time. The entire attack report can be exported into CSV, PDF, or XLS format. Sn1per Professional provides notifications for scan and host status changes, URL and domain changes, and new vulnerabilities discovered.
#11 Spyse
Spyse is one of the leading cybersecurity data and internet assets registry data providers. It collects all the publically available data about servers, devices connected to them, websites, and their owners. The gathered data is analyzed to discover security risks and implicit connections between those entities. The premium users also get real-time search and third-party integration. Spyse API has a huge variety of search operators and detailed documentation. You can integrate the API into your recon pipeline, cybersecurity solution, or connect to the database for real-time data acquisition.
Another notable feature is the Bulk Search that is designed to search for multiple targets at once. Upload a file or submit any text and it will search its contents, find all domains, IPv4 addresses, and show the results of each of them. With its advanced search engine, execute finely-tuned data search queries using a rich set of filters. Find, share or download the data you need in just a few clicks.
#12 LeakIX
LeakIX is a search engine that allows you to index open hosts on the internet and focuses on listing the databases or table names. It has many pre-built plugins that you can choose for a specific operation like GrafanaOpenPlugin to connect to open Grafana instances and listing their dashboards and permissions. Other plugins let you connect to open ElasticSearch, extract system information, get index list, collection list, table list, configuration list, and much more.
It establishes a real-world persistence inside your infrastructure and provides real-world indicators of compromise to your incident response team. You can also use a browser pivot to apply two-factor authentication and access sites as your target. All in all, LeakIX is a useful indexing tool that you can consider among its alternatives.
#13 Reposify
Reposify is a tool that allows you to manage your external attack surface and reduce digital risks. This helps you see your unidentified and unprotected possessions and shadow IT risks in real-time before attackers exploit them. The tool is designed to focus on what really matters by automating all the processes. You can measure threats, vulnerabilities, impact, and risks related to exact cyber-security events by rapidly reacting to the integration of both offensive and defensive security. Reposify uses a progressive interface that supports rapid reconfiguration to adapt exploit codes and benefits to the constantly evolving threat environment.
Reposify tool lets you quickly modify, reconfigure, or add new exploits to the framework. Exploit Pack provides you with a unique set of features to assist you during the exploitation process. In short, you can replicate real-world attacks and use the network before hackers do.
#14 BabySploit
BabySploit is a penetration testing toolkit written in Python. The aim of this tool is to make use of many complicated and large frameworks. The easy-to-use UI makes it easier to learn, even for beginners. Some highlighting features include information gathering, exploitation, post-exploitation, brute-forcing, phishing, cryptography, DNS lookup, Cloudflare bypasser, and much more.
BabySploit uses ConfigParser in order to write and read configuration. Your configuration file is automatically generated and located in one place. You can manually change configuration settings by opening up the file and editing with a text editor, or you can use the set command to set a new value for a key.
#15 Natlas
Natlas is a program that allows you to identify vulnerabilities with scaling network scanning. The aim is to identify the exposures and make sure no one is running the SSH with password auth enabled. Other than that, it also looks for exposed smb, resync shares, and nfs. You can also look for expired SSL certificates or weak SSL ciphers being used. As Natlas uses a popular Nmap port scanner, you can easily use any default Nmap script in your scans.
#16 SearchDiggity
SearchDiggity is a primary attack tool for Google’s hacking diggity project. It is a sort of Windows GUI application that provides a front end to the most recent versions of Diggity tools. The tools include, BingDiggity, GoogleDiggity, Bing LinkFromDomainDiggity, DLPDiggity, CodeSearchDiggity, FlashDiggity, PortScanDiggity, MalwareDiggity, SHODANDiggity, NotInMyBackYard Diggity, and BingBinaryMalwareSearch.
The input dictionary file contains queries that allow users to uncover SharePoint-specific vulnerabilities exposed via the Google search engine. This dictionary helps evaluators find exposures of mutual SharePoint administrative pages, web services, and site galleries that an organization typically would not want to be made available to the public.