Veriff
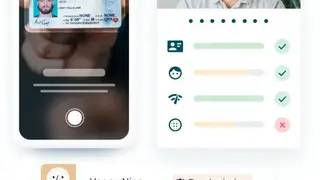
Veriff is identity and personal information verification software that enables users to verify their identity, complete social security and background reports, credit checks, and more. Its patented technology, Verification Intelligence, empowers users with the most advanced biometrics, liveness detection, and machine learning capabilities on the market. Veriff’s I.D. verification technology allows federal, state, and local government agencies, e-commerce businesses, and accounting firms to verify identities faster and more efficiently than ever before.
The goal is to create a fairer marketplace by providing companies access to the richest pool of consumers while giving consumers unprecedented access to valuable offers without revealing their personal information. Veriff makes it easier to do business with those you don’t know by verifying their identity and enriching the information provided by them. In short, it bridges trust between you and your customers or businesses you do not know by using the most advanced machine learning to verify a user’s identity in the most cost and time-efficient way.
Veriff Alternatives
#1 Mitek Mobile Verify
Mitek Mobile Verify is an Identity verification solution that delivers I.D. document capture and instant verification on both Android and iOS devices. It also enables banks and merchants to onboard new customers by capturing their identification documents on smartphones, eliminating the need for a home visit or in-store photo I.D. This can help speed up transactions and reduce identity theft losses by preventing criminal activity such as identity fraud.
Mitek Mobile Verify provides complete control over the identity verification process by giving businesses control over data collection, including where the data is captured and stored. It stores users’ personal information is secured, encrypted data centers. Mitek Mobile Verify does not require any changes to merchants’ existing point-of-sale (POS) systems and is compatible with all payment terminals and POS software. It eliminates the need for your customers to show physical I.D. documents or wait in line at a bank.
#2 Jamf Connect
Jamf Connect is a Mac authentication Streamlining and identity management platform that helps organizations manage Apple devices, authorize access, and streamline the overall user experience. It is one of the first sign-in services that bring people and products together on a single platform. It enables organizations to scale their Mac deployments, evolve identity management, and improve the Mac experience with Mobile Device Management. Streamlining administration and identity management, Jamf Connect allows customers to manage endpoints and users through a single, modern platform.
The solution also enables IT administrators, to spend more time delivering proactive services and less managing infrastructure. Jamf Connect is designed for organizations of all sizes with Apple products deployed in the enterprise, including education, healthcare, government, and small businesses. Admins can track and monitor what devices are being accessed, from where and by whom, providing peace of mind that both device and corporate information are protected
#3 IDology
IDology is real-time identity verification and fraud prevention platform that streamlines the Know-Your-Customer (KYC) process for financial institutions, banks, payment service providers, and merchants. It offers comprehensive and secure identity verification and fraud detection designed to streamline the onboarding process, enhance the customer experience, and minimize operating costs associated with regulatory compliance.
By leveraging advanced biometric technology and a patented Intelligent Identity Management platform, IDology provides connections to multiple sources of identity in order to quickly and confidently verify and authenticate clients. The platform is used by the top financial services firms, payment card issuers, retailers, and travel companies across the globe. IDology’s Velocity feature automatically detects the rate of occurrence of identity attributes and can be used to escalate or stop numerous repeat transaction attempts in order to deter fraud.
#4 Microstrategy Usher
Microstrategy Usher is an enterprise digital identity platform to help organizations digitally identify their customers, employees, and business partners. It includes several capabilities that significantly expand the opportunities to engage with end customers and business partners beyond the login. The solution seamlessly blends authentication, authorization, and consent into one simple service, eliminating the complexities of single sign-on, password management, and federation. Single sign-on enables your customers to authenticate once and access all their business applications without entering usernames and passwords, which are transmitted over a secure and trusted channel.
Microstrategy Usher includes pre-built integrations with all major SAML 2.0 products, including Salesforce, Box, and NetSuite. Eliminate the need for a password by using biometrics or authentication based on a hardware token. Moreover, its multi-factor authentication solution provides additional security by validating your customer’s identity across three different channels: Web, mobile, or hardware token. With Microstrategy Usher, organizations can rapidly onboard new users, collect and manage identity attributes in real-time, enforce security policies and ensure the highest level of compliance.
#5 AU10TIX
AU10TIX is an identity verification solution that protects online and mobile users from fraud by using Artificial Intelligence to create unique predictions and detect anomalies that are still invisible to the naked eye. With this platform, online and mobile users can be sure their identities will not be stolen or compromised. With its quick access, high accuracy, and power to initiate real-time transactions, AU10TIX provides a solution to one of the most challenging problems businesses face today.
By verifying users’ identities, you can comply with laws, regulations, and industry standards related to identity verification. It delivers an automated background check for financial companies, helps employees show proof of employment for the benefit or pension providers, allows people to prove their identity when applying for a passport or driving license, can be used by charities to prevent money laundering and the financing of terrorism, and offers a trusted network of people who can vouch directly for a person’s identity.
#6 Verifai
Verifai is an identity verification software solution that lets users verify a user’s identity using facial recognition and biometric data. Unlike other forms of I.D. like passports or social security numbers, facial recognition has the ability to identify someone in a matter of seconds using just a photo. This makes verification fast and frictionless. The software analyzes thousands of data points in milliseconds, enabling businesses to quickly determine whether or not an online user is who they say they are.
Companies using Verifai flag 5x fewer users for follow-up review than legacy solutions, allowing them to spend more time on the users most likely to be fraudulent. The company also employs a proprietary algorithm that further accelerates the process by deducing from new data whether an account is not likely to be fraudulent by design. With this solution, you will experience a drastic decrease in fraud rates, an increase in customer trust and retention, and enhanced security by providing the sensitive information to only those who have proven they are who they say they are.
#7 Acuant
Acuant is identity verification, document authentication, and fraud prevention platform that helps businesses to verify an applicant’s identity, check their work, and prevent identity fraud. The company employs document fingerprinting, geolocation, and biometric technologies. Its services include providing text message-based alerts for card fraud, identity verification for international remittances, passport verifications for foreign nationals in three minutes or less, international money transfers, and risk management solutions.
Through the use of AI, machine learning, and multi-factor authentication, Acuant has developed a platform that allows its customers to bring trust and transparency to any business or application. Whether it’s the world’s largest bank or an online lending platform, its customers have increased accuracy and reduced friction across the entire customer lifecycle. Anywhere where identity is in question, Acuant’s solutions play a significant role in investigating, mitigating, and preventing fraud.
#8 CloudApper EMR Link
CloudApper EMR Link is a Patient Identity Management Application that allows easy and transparent access to patient healthcare records to all authorized healthcare employees regardless of their location. All records are stored on the cloud, and access is controlled via authorized logins. Users may log in on any device and view their patient’s demographic information and health care events using the web or smartphone applications. CloudApper EMR Link provides full confidentiality of patient health data by only allowing authorized healthcare employees to access patients’ information.
All patient information is stored in the cloud and is encrypted in transit. The application does not store any personal health information of the user on a local hard drive or server. Get rid of the age-old problem of information burnout with the EMR system & access your required information using the interactive search bar. All in all, CloudApper EMR Link is a great platform that you can consider among its alternatives.
#9 Yoti
Yoti is a digital identity platform providing seamless experiences by securely connecting people to things online. It combines accredited government verified I.D. documents with real-time verified attributes, allowing people to prove their identity using their smartphone or computer. It offers an alternative to passwords and pins that creates trust in e-commerce and mobility applications, ultimately saving users time and money. The solution combines online verification and identity checks with privacy controls and data protection so individuals own their digital identity and can share only the information that matters to them.
You can use this for anything from validating your identity for employment or proving eligibility to sign up for a new online service to proving your age on social media. You can also use Yoti for something much more personal; to give your loved ones greater peace of mind and to add an extra layer of security and protection when buying goods or booking travel by attaching Yoti to an existing card or driver’s license.
#10 authID.ai
authID.ai is the leading enterprise Identity verification solution that allows developers to verify the identity of the customers accurately and, at the same time, makes it easier for the customers. It expands on the traditional verification methodology of user name, password, and date of birth with behavioral biometric attributes like typing cadence, mouse speed, and mouse movements across the screen to create a more secure I.D. The solution leverages Artificial Intelligence and Machine Learning to provide enterprises with a powerful Identity Verification solution at a fraction of the cost of traditional solutions.
AuthID.AI also provides web and mobile application developers with an easy-to-integrate user verification solution that provides an enterprise-level of security. Moreover, you also get a secure yet easy-to-use technology that offers verified identity information, including email addresses, phone numbers, physical addresses, and social media profiles. The API is currently certified for production use by Google and Facebook.
#11 PXL Vision
PXL Vision is a digital identity verification platform that enables organizations to digitally verify a person’s identity instantly and cost-effectively, without requiring users to download any additional software or hardware. The technology behind PXL is a patented cloud-based video analysis platform with advanced computer vision technology. The solution is based on video recordings of the interview, processed by advanced algorithms and biometric recognition mechanisms. The solutions can be tailored for specific needs regarding user experience, data retention, and other variables.
This technology-driven solution increases security and reduces fraud while increasing efficiency and customer satisfaction. It does this by using biometrics as the digital identity of a person and developing advanced algorithms to match this identity. Its SDKs and APIs offer a simple, standard interface for quick and easy integration. The dynamic workflows automatically adapt to your business process and use case without the need for multiple integrations.
#12 Alice Biometrics
Alice Biometrics is an online identity verification solution that uses a patented, state-of-the-art artificial intelligence algorithm to validate the identity of an individual within minutes on any digital media platform, including mobile and desktop. The platform works with any smartphone and allows users to capture an image or video of their face that is then validated against a database and provides proof of identity within minutes.
The application was built to conform to current national and international regulations and provide legal compliance. By adding biometrics data to the identification process, it enhances the security of personal data being collected. Alice Biometrics provides a new way to register and verify one’s identity quickly, easily, and securely, providing an easier way to access e-government services and reduce identity theft. All in all, Alice Biometrics is a great platform that you can consider among its alternatives.
#13 EMDYN BioTrace
EMDYN BioTrace is an online identity detection and validation system that enables enterprises to detect sophisticated cyber breaches early and proactively manage risk prior to material impact or regulatory fines. The solution can be used in a wide range of industries, from small to medium and large enterprises. With this platform, you can analyze any kind of threat and future incident. The data is accumulated from various sources to provide a more accurate data set based on AI.
Its high-grade geolocation data, visualization tool, and deep search exploration tool allow for biometric scans and object recognition and provide you with detailed insight into processed data. It delivers a set of capabilities to help you make better-informed decisions using a series of modules. The process employs, takes three steps: firstly, to identify the key data relevant to the situation from as wide a range of sources as possible, then to analyze it in depth forensically, and finally, to determine a course of action.
#14 iProov
iProov is a biometric identity authentication platform that can be used to verify proof of identity at multiple touchpoints using face, finger, and voice biometrics. It acts as a secure digital passport for digital financial services and eCommerce users. It can be used in high-end applications such as Banks and financial institutions, Lending and online payments, Government enrollment, Education and digital certification, Private social networking, and email providers. With iProov, users can verify their identity by simply swiping their fingers, snapping a photo of their face, speaking into the app, or by using other machine-learned features.
Users don’t have to remember a password, fill out forms, or download an app. It enables simple, secure step-up authentication to provide extra protection on transactions with an increased risk or value. The process of applying online for visas and other immigration documentation has been revolutionized by technology. Thanks to iProov, governments can now securely verify the genuine presence of remote applicants within seconds to automate administration.
#15 Oracle Identity Governance
Oracle Identity is an online governance solution that allows complete access to governance and comprehensive optimization of identity for actionable insights and rapid compliance. This software delivers users administration, identity intelligence, and privileged management and provides versatile actionable insight powered by rich analytics. This software comes with automated controls, risk-based analytics, and beneficial dashboards that enable rapid enterprise risk.
Cloud application service provides free account management and administration services that allow you to get complete access form shared accounts, and it also offers many abundant audit trails that ensure vast security and compliance for sensitive systems.
Oracle identity governance permits an undefined user experience and gives self catalog and drag-and-drop services, and more. It is establishing a great integrated system with bolster security and lower TCO and it lets you automatic optimization that identifies high-risk users.
#16 OneLogin
OneLogin is a leading Identity and Access Management software specially designed to simplify business logins while improving the security and efficiency of your systems. Thousands of businesses and individuals use the solution because it is fast and easy to implement and helps in streamlining numerous of a user’s workflows and processes, resulting in enhanced productivity without compromising security.
With the help of OneLogin, all applications, users, and all the other devices are unified in a deeply integrated cloud-based system. It makes IAM (Identity and Access Management) fast and easy, providing users with the correct implementation of your policy while reducing the load of your IT and make it work on its identity first strategy.
The system gives your staff access to the applications that are certified policy compliant. All the devices in your business are secured as the solution brings enterprise agility coupled with secure application access. This security is fully applied across the entire network and organization, including corporate desktops, web applications, and mobile devices. OneLogin is a simple but powerful application that manages your complete system. It also has a list of prominent features that make it more interesting.
#17 AuthAnvil
AuthAnvil is another IT security application specially designed to help IT teams keep their networks, infrastructure, and devices secure all the time even during non-working hours. It is one of the best platforms that comes with lots of advanced tools and services that make it better than others.
The solution takes off the burden of managing passwords for the shoulders of your IT department and allows them to devote more time to ensuring that your networks are all up and running, and your data is fully secure. The best part of the application is that it combines password management, single sign-on, and multi-factor authentication abilities, efficiently taking out password glitches that plague both IT admins and users.
With the help of this application, users can quickly access their accounts, files, and systems without having to remember their passwords.
The software includes core features such as integration, two-factor authentication, single sign-on, secure remote access, universal directory, and much more. Like the other similar platforms, it also has different price plans, including AuthAnvil Enterprise, AuthAnvil Enterprise 2FS, AuthAnvil MSP Protect, etc. Each one has its price and core features.
#18 TeamPassword
TeamPassword is an all-in-one cloud-based password management system for creative agencies, software design, and development teams. Compared to it from Okta, it is a bit different and offers lots of advanced features that make it better than others. The solution provides efficient techniques to accomplish various passwords and logins management.
It also enables teams, groups, and businesses of all sizes to easily manage and share passwords for tools, apps, and services required to keep projects moving. TeamPassword allows users to describe the level of access to each password, create team passwords, get notifications, and more. It is a quite simple application that helps users to manage, add, and share internal client’s passwords.
With the help of this solution, companies are also able to communicate with each other to discuss their projects. One of the most addictive parts of the application is it provides a secure built-in password generator that allows you to create unlimited secure passwords.
The feature is strong enough to allow users to create secure and randomized passwords as they set up a shared or private login. Like the other similar solutions, it also offers a massive list of prominent features that make it better than others.
#19 WebTitan
WebTitan is a web content filtering and malware protection platform specially made for Hotspot and WiFi providers managed service providers and retail and public organizations that are offering WiFi access. It is easy, and one of the best deployment option, which can be either in the cloud or on-premise the solution allows businesses and organizations to protect their employees and customers while they are online.
It provides users with the ability to prevent access to unsuitable and inappropriate stuff, which includes pornography, hate speech, and all the other banned stuff. WebTitan enables to control the content and material that their customers and guests can access, ensuring that they are protected against all kinds of cyber threats like viruses and phishing.
The platform comes with comprehensive reporting tools that assist organizations in crafting policies to build a safe environment for employees and end-users. Like the other applications, it also offers lots of prominent features such as DNS-based solution, multiple filters, live view of user browsing activity, PDF and Excel export option, automated scheduling and behavior-based reporting, etc.
#20 Teramind
Teramind is another employee monitoring solution and computer security platform that tracks what employees are doing on computers as well as protects the network from potential threats like information theft etc. It is one of the best alternatives to Okta and offers all the similar service with some new feature that makes it better than others.
With the help of this solution, all the companies can isolate suspicious activity and pinpoint probable security hazards and monitor employee efficiency and productivity. The solution also assists IT security and owners to decrease security occurrences by delivering them with real-time alerts. On top of that, Teramind locks users, and devices seem to be a threat to the integrity of the company.
One of the most exciting and enjoyable things about this application is that it offers employee activity history playback that allows companies to interactively review their employee’s activity at the end of the day or at any time. Email monitoring, Keystroke logger, file tracking, automated behavior rules, and project management integration are also features of the platform.
#21 ActivTrak
ActivTrak is one of the best HR or employee behavior analytics platform that allows employers to monitor and manage what their staff is doing and the duration of the time they work on it. The software is invisible on computers and not show any notification or another related thing even in the task manager.
It is a powerful employee behavior analytic tool that also offers lots of tools, helps you to manage their work such as website disabling, direct user monitoring, automatic screen capture, and lots of other interesting things.
ActivTrak includes core features such as push notification, insider threat detection, real-time employee monitoring, remote screen viewing, and malicious website blocking, etc. It also has different price plans; each plan has its own cost and core benefits.
#22 Gigya
Gigya is a customer support software created with the intent of fusing and using social media channels as the avenue to garner more loyal customers and increase productivity. It is a commercial solution, and you can access it anytime, anywhere around the world. With Gigya software, networks are equipped with capabilities and functionalities, which enable them to utilize social registrations that turn spike up your customer value and open more channels for communication to social engagement. Gigya is one of the best solutions that helps you to create better business relationships by turning visitors to your network site into loyal and engaged customers.
The solution also allows you to register and identify clients across your websites and applications. After register a customer, you can also organize and manage the profile data of your customers. Just like the other similar solutions, it also has a list of prominent features that make it better than others. Its most famous features are social login, analytics, identity access, gamification, consumer insights, and rank, etc.
#23 Janrain
Janrain is a CIAM (Customer Profile and Identity Management) software based in Portland, Oregon, established in 2002. It is the first choice of global enterprises for a mission-critical customer identity and access management. Janrain delivers all the real-time identity management, activation capabilities, and security that allows seamless and safe customer experience while providing your organization with deep customer insights.
With the help of this application, business leaders get to market faster, scale globally, and accelerate time to value by 2X with the turnkey customer identity and access management solution. Its native cloud architecture is design to create customer trust and product your company’s reputation with strong privacy and governance capabilities.
Janrain is best for almost all the leading industries, including Travel and hospitality, healthcare, media and publishing, Omnichannel retail, and much more. Another great thing about this application is that it offers a customization option that allows you to add your setting depending on your business.
#24 Symplified
Symplified is an Identity-as-a-Service software that allows IT organizations to simplify user access and control over application usage and meet security and compliance requirements. It is another alternative to Okta and provides all the similar services, including identity and access management, strong authentication, mobile device support and centralized revising, etc.
The solution also allows convenient access to any cloud or not-premise application through the unfiled, customization SSO portal and delivers a single-tenant control point in IDaaS. The solution also offers lots of marketing tools that increase productivity and manage the complete system. Symplified includes core features such as API, monitoring, SSL security, auditing trail, authentication, website security and compliance management, and much more.
#25 Bitium
Bitium is an Identity Management platform for IT leaders that allows end-users to access all of their cloud software accounting using the single set of login credentials. It can integrate with cloud apps using the SAML for improved security. Bitium was introduced in 2012 with aims to give growing companies the ability to manage access to all of their web-based applications such as Google Apps and Office365 as well as social marketing and CRM, collaboration, and macerating tools.
It is a simple but powerful application that allows companies to extend existing their existing directory structured to cloud applications. Just like the other similar solutions, it also can integrate with Active Directory, Google Apps, LDAPS, and lots of other on-premises directories to enable centralized user access and management. The solution comes as the alternative to Okta and offers all the similar services with some new features that make it more interesting.
#26 SmartSignin
SmartSignin is one the best and secure way to manage access to your cloud applications for SSO for your partners, customers, or employees, across multiple devices. It is simple and easy to use app that has millions of users around the world who can manage their work secure, simple, and fast.
The application makes life easier for employees that allows just one-click login to every application your organization uses without any pre-integration or collaboration with most other solutions. It allows you to integrate your AD/LDAP and other identity stores for easy syncing of users and to access all the applications you use in the cloud.
The great thing about this platform is that it supports lots of other identity stores, including Google Apps, Office365, and SalesForce, etc. This complete system raises productivity, empowers your company, and gets rid of security liabilities.
Compared to all the other similar solutions, it offers lots of core features that make it more interesting such as too many passwords, bring your device, security breaches, strong authentication, and active directory, etc. Enterprise, SMB’S, and Single User these are three different price plans; each plan has its price and core benefits.
#27 CyberArk Privileged Account Security
CyberArk Privileged Account Security is a leading account management solution designed to ensure the safety of your privileged accounts, password, and devices, etc. It is a powerful system that helps organizations to meet stringent IT and compliance standards with a strong focus on privileged password management.
With the help of this system, enterprises and organizations can adhere to audit and compliance policies and standards that enable them to identify the risk that advanced persistent threats entail quickly. This flexible system also makes it easy to enforce an enterprise security policy around behaviors surrounding privileged accounts.
Audit needs and requirements range from the number of times a privileged credential should change to how complex a password should be, among others. CyberArk Privileged Account Security also allows you to generate comprehensive audit reports on a variety of account access and document every privileged activity for audit-proof and forensic analysis. Cloud and virtualization security, DevOps security, windows security, and confidential file security are also features of the system.
#28 Castle.io
Castle.io is a world’s number one IT security solution designed to secure next-generation cloud services with modern algorithms and lots of other enterprise-grade security protocols. The solution is automatically tracking occurrences in your mobile apps, websites, and cloud-hosted services as well as analyzes patterns and indicators such devices and locations inconsistency.
It is not just an IT security system, but it also looks at users’ behavior to detect all the malicious activities. Once you can activate and events are identified and revealed, you can utilize its webhooks, REST API, and Slack motivations to create workflows of your security. Castle.io is also known as the solution that enables B2C and B2B, a very powerful and robust security solution that helps you to secure your products, whether it is a mobile app, e-commerce store, or a bitcoin service.
It is a flexible security system that can be plugged into any environment at any level. With the help of this solution, businesses can monitor their complete system, including mobile apps, websites, and all the other customer-facing products and track any source in minutes. The solution also includes core features that make it better than others.
#29 Applozic
Applozic is a commercial solution that offers businesses a chat and messaging SDK and API toolkit, allows them to integrate messaging into their application without the need to create a new infrastructure. There are lots of similar IT management solutions available to use, but it introduces lots of new services and features that make it better than others.
The Applozic API is RESTful, leverage HTTP methods over SSL, and also support JSON data types. With the help of this system, it makes it easy to reach out and interact with image, file, location sharing, and auto/video conversations. The software has implemented in multiple industries and sectors, including E-learning, Healthcare, Marketplace, Travel, and Lifestyle, etc.
Applozic is also known as a fast and easy integration without the need to have a server setup. The user can receive native clients SDKs for iOS, Android, and Web. Just like the other similar solutions it also offers customization feature that enables lots of room for creativity and flexibility, the user can also be able to customize the theme of the setup, icon easily and chat bubble icons, etc. Applozic also has a list of core features that make it better than others.
#30 YouTrack
YouTrack is a simple but powerful IT Management solution that combines commercial browser-based bug trackers, project management capabilities, and issue trackers into one neat and comprehensive package. It is a product of JetBrains and thousands of users around the world who can use it to enhance their IT system.
The solution offers a query-based issue search functionality with auto-completion. It allows users to manipulate issues in the batches, customize all the set of issue attributes, and create a custom workflow. As compared to all the other similar solutions, it has a robust search function that allows users to get the information they need they need quickly.
It also introduces a shortcut that significantly accelerates mundane processes. With the help of this IT management solution, users can get insights and track the progress of every project with lots of reporting tools that allow them to make better business decisions and implement effective strategies.
Edit Images in place, search queries, star issues, completion and highlighting, customization, time management, filters, tags, mobile interface, and multiple drafts are also features of the software.
#31 SpatialKey
SpatialKey is a leading Business Intelligence solution that gives business insurers the efficient business processes and true analytics they need to thrive in today’s business. It is a quality leader when it comes to insurance analytics, visualization, and delivers real business value with its purpose-built applications.
SpatialKey is also known as a complete solution for companies that deliver unmatched performance, visualization, and flexibility to access analytics, trends, and pattern without any expert guidance or training. Like the other similar platform, it also provides a complete suite of unbiased and unprecedented analytics features to authorize your company with risk intelligence that not improve your bottom line but also your resiliency.
With the help of this solution, companies realize the overall potential of their data and manage their whole system. SpatialKey includes core features such as event analysis, accelerate underwriting decisions, advanced risk selection, exposure management, and much more.
#32 InVision
InVision is a simple and easy way to create a design and test prototypes, business models, and a variety of designs for any device. It is a commercial solution that has more than 1.5 million users around the world. With the help of this application, you take any sketch or design from multiple sources, including Photoshop. After taking a design, it allows you to transform them into a stunning design that can be applied and tested on any device.
You can easily take the image to InVision’s system with its amazing drag and drop functionality or use integrations with Dropbox and Google Drive into the syncs files smoothly. The application introduces a clickable prototype that makes it easy for designers to be on the same page with each other, see the flaws, and determine the enhancement needed.
Collation is one of the strongest attributes of the solution; designers can work individually without any hassle and easily communicate with fellow designers and their clients for faster ideas, feedback, and more. User testing and research, real-time design meetings and whiteboarding, design sharing and presentation, project management, and drag and drop are also features of the solution.
#33 Scalyr
Scalyr is an all-in-one IT management solution created by Google Docs creator, and it brings the ease and speed found in consumer applications to a robust server monitoring tools. It is also known as a platform for high-speed server monitoring and log management.
The application’s log aggregator module collections all applications, processes, web, system log, and manages their volumes by filtering for sensitive or noisy logs before releasing them to the server. It is one of the best alternatives to Cylance and offers all the similar services that make it better than others.
The solution analyses and summarize data from logs into the interactive reports and visualizations. Just like the other similar applications, it also has a robust dashboard that allows you to quickly view process and server metrics as well as web traffics.
Scalyr also includes core features such as built-in diagnostic tools, event logs, mail server interactive reports, rest alert, web mentoring server groups, and real-time log monitoring, etc. Another most addictive thing about this solution is that it offers a customization option with lots of advanced tools to deliver a complete experience.
#34 Cylance
Cylance is an endpoint security platform that detects, prevents, and blocks threats. It is a simple but powerful solution that has millions of users around the world who can use it to secure their IT systems. With the help of this application, IT infrastructures are duly protected against different kinds of threats because of AI (artificial intelligence) that helps provides more robust protections than legacy antivirus. It is also known as accurate, effective, and efficient protection against all kinds of advanced cybersecurity attack techniques that try to infiltrate a company’s endpoint.
The application also offers real-time protection for businesses that attract more audiences around the world. One of the best things about this security system is that it equipped all the primary tools that can notice and prevent threats, no matter which techniques are used to deploy them. Cylance includes lots of prominent features such as predictive analysis, independent malware execution control, lousy binary prevention, script control, and much more. It also has multiple price plans; each plan has its own cost and core benefits.
#35 Symantec VIP
Symantec VIP (Validation and ID Protection Service) is a leading, user-friendly cloud-based authentication service that allows enterprises to access networks and applications without impacting productivity. The solution delivers three major services that make it stronger than others. Such as Proximity Unlock that enable you to unlock your computer without typing password over Bluetooth Low Energy, Two Factor Authentication that serve more than a password allow VIP for two-factor authentication website like PayPal and other.
Credential Wallet allows you to scan a QR code to security generate security codes for your favorite website like google. Symantec VIP also introduces lots of advanced technology and features. The platform’s most prominent features include a user-friendly interface, push authentication request, proximity, security codes, anti-cloning, and much more.
#36 Cisco IronPort
Cisco IronPort is a leading provider of messaging security appliances that are focusing on enterprise spam and spyware protection. It is also known as an email and a web security gateway and management product currently referred to as Cisco Email Security and Cisco Web Security. It delivers world-class email and web security that IronPort customer care used to.
The program’s security products and technology include industry-leading threat mitigation, confidential communication, and policy control and management solutions. It is a complete solution that comes with all the primary tools and services that decreased the attack surface from users downloading malicious files. Cisco IronPort includes prominent features such as malware protection, block non-business-related websites, easy to understand and reduce confidential business leaks, etc. It is a commercial solution and has different price plans.
#37 Auth0
Auth0 is all-in-one software which provides authentication and authorization management platform which integrate with every type of digital devices available in the market. It also works on website devices mobile, IoT devices, laptops, and apps. It consists of interesting modules, and it is mostly utilized for Enterprises supporting the B2B, B2C, and B2E for universal identity.
Auth0 also provides you a robust architecture and comes with improved security, which saves your data and transaction in highly encryption form and provides various modules for login, and it prevents 1.3 million malicious logins that are trying taking your identity.
The key aspects of the platform consist of many interesting modules. Some of them are universal login flow, customer domain, audit logs, universal login, SMS port, white-label manufacturer, brute force protection, duplicate amount consolidation, and much more.
Auth0 also provides an adaptive multilayer security password, less authentication, customizable login pages, advanced analytics, and reporting facility, which is done in real-time, and much more. The interface is easy to use, and it is highly customizable, and it shows all the changes on the platform, and you can integrate every type of data on the platform and security in the best way.
#38 Keycloak
Keycloak is a software which is providing identity management, asset management, and single sign-on interface for every user to integrate their product and utilize all its services. It is an open-source platform and gives you tons of facilities in the management aspect, and it also provides two main components, which involve the server and application adapter.
It gives different documentation tools, app security extension for third party access, and much more. Keycloak has various options to choose from regarding editing and merging the file. The core feature of the platform includes user registration, social login, single sign-on and sign-out protocol across all application integrated into the same platform, two-factor authentication, LDAP integration, multi-tenancy with per-realm customizable skin, and much more.
The interface is easy to use, and the software provides a sophisticated interface for both desktop and cloud-based modules. The central aspect of the platform offers the user to interact with the sign-up feature and Keycloak itself easily is sponsored by Redhat, which is known for its security aspects.
It gives identity blocking, and social login for its subscribe users. It also provides different clustering theme integrating the platform into extinction password policies, high-performance identity brokering, centralized management adaptors, standard protocols, and much more.
#39 SiteMinder
SiteMinder is an online marketing and management solution designed especially for individual hotel owners, hotel chains, and partners as well. It provides the facility to improve the two-way connection across the destinations of the globe with ease by helping the hoteliers in efficient and productive channel management.
It is a cloud-based platform that reaches the prospects on social media and creating mobile-friendly websites. It helps you to capture the maximum number of potential clients with a comprehensive product suite and convert them into customers quickly. It reduces the workload form the hotel owner’s shoulders and allows them to make an online booking for available rooms.
The core features of SiteMinder includes real-time management and reporting with performance, customizable templates for creating websites, connection to popular booking channels, statistics on distribution and production, and many more. It gives real-time payments using payment gateways and integrates with popular products & services.
It is available on mobile and desktop platforms such as Windows, Linux and compatible with small, medium and large-sized businesses. It offers a free trial and secures paid plans to unlock the pro features such as fully customizable internet booking engine, multi-language support and currency, and full control & automation.
#40 FireMon
FireMon is an automatic solution for security purposes through the comprehensive delivery of blueprint and streamlines policy management. It features trusted accuracy, gold standards, proactive, and continuous compliance.
It is the only way that closes the gap between security and businesses, and you can get visibility and control by reducing the visible gap from the hybrid system through situational awareness. Its resources include a newsroom, blog, and resource library that gives a complete guide to your solution.
Its priorities vulnerability includes optimize management, define a path to remediation, and analyze network traffic flows and lets you automate with confidence. Its primary features include policy optimizer, Rumeta, risk analyzer, and security manager. The solution also offers global services that include professional service and support services and providing training services as well. The zero automation feature includes hands-off automation, security intent, and golden rules.
#41 Okta
Okta is the world’s leading independent provider of identity for the enterprise. It is also known as the adaptive security platform that protects your data. The Okta Identity Cloud allows companies to both secure and manage their experiences. With the help of this application, its customer can easily and securely adopt the technologies they need to fulfill their missions. It is a simple and easy-to-use platform that has millions of users around the world who can securely connect to the technologies and services that allows them to do their most important work.
Okta is a subscription-based platform that requires an email address and all the other information to subscribe. It has different price plans; each plan has its own cost and core features. Some prominent features are supported by mobile device management, reporting, geographic functionality, attribute information, secure access to APIs, and creating an intelligent contacted world, etc.
#42 EventSentry
EventSentry is a complete combination of real-time event logging monitoring, system health, and Network monitoring systems. It offers tons of tools and allows the user to quickly get every type of information regarding any event integrated or change in the system. It also gives you the security event and logs normalization with the correlation engine.
The main functionality of the platform is to provide a comprehensive analytical reporting and real-time monitoring system that you do not find on any other monitoring services. It also provides the security feature that is handled in the monitoring as diet and health system and monitoring provide the system performance reporting regarding every several aspects of the integrated modules.
The platform provides complete filtering and detects the issues quickly. It works well for businesses and various sizes of organizations. EventSentry offers many features like customizing the dashboard, filter threshold, performance monitoring, disk space monitoring, recurring events, compliance collector, service log, file monitoring, network monitoring per-host license, and more. It also offers Windows-based software and gives a cloud-based solution.
It also offers environment monitoring that is directly attached to network-based sensors, provide live agent support, multi-tenancy monitoring, and much more. EventSentry also provides a trial version, and you can get the subscription module for less cost.
#43 Centrify
Centrify is a platform that offers security services against cyber-attacks and threatens the IT infrastructure of cloud or on-premise applications of companies. The platform keeps the enterprise’s internal and external users as well as its privileged accounts from cyber threats that breach the data. The platform provides services to enterprises in managing and securing the identity of all users, including customers and business’ employees.
Centrify securely manages and offers access to infrastructure with a simplified shared account password to all users through its Enterprise Password Management. Moreover, users can easily create accounts or automate app requests with workflows through its automated Account Management service. Some of the essential features of Centrify are ISO Compliance, Risk Assessment and Management, Architecture Governance, VPN, Data Mining, and Multifactor Authentication.
The platform prevents unauthorized access to trusted computing resources and data by providing users with server isolation. The platform offers a free trial and comes with a paid version only. It is compatible with all kinds of platforms, from web-based to Windows or mobile devices. Training is provided in person and through webinars and documentation, while technical support is available during business hours and 24/7.
#44 OpenID Connect
OpenID Connect is an identity verifying platform which allows the users to verify the identity of the End-user by an authorization server. It can provide necessary profile information to its clients about the end-user based on the authentication he/she is performing. The platform helps the client of all types, either web-based or mobile, to receive information on their authentication session and end-user performing those sessions.
The working is simple; when a user signs in to Auth0 using their Google account, it sends an authorization request to Google, which asks the user to verify the account, or it automatically verifies it. As soon as the user ID is authenticated, Auth0 can retrieve information from ID token to invoke a Google API.
OpenID Connect comes with various documents such as session management, which defines how to manage OpenID Connect sessions. Lastly, it provides front-channel logout, which describes other different mechanisms and explains robust signing and encryptions.
#45 Virtual Badge
Virtual Badge is a workplace and identity management solution that enables users to users their smartphones as their identity badges, which save both time and money. It comes as both mobile and web-based software, which allows organizations to solve the hassle of identity issues in workforce management.
The platform uses its smartphone application to issue and display ID cards and does not require any separate hardware other than the phone itself. It enables the users to customize the badges in that way they want with advanced security and validation features. Moreover, organizations can control who can get a badge all through their application.
Employees just have to download the app and request a badge, and organizations can approve that request through the app. Moreover, users can scan the badge to track attendance and time of each employee. Lastly, scanned information is downloadable and provides a GPS tracking feature of employees.
#46 Avocode
Avocode is an online platform that enables the developers to collaborate, design, and discuss coding websites and mobile apps, all through a single platform. The platform is appreciated by most of the agencies as it brings all the stakeholders in the collaboration and design processes. It enables the clients and team members to review and provide feedback about the design right on the platform instead of emails.
Avocode provides a unified login endpoint through its Single Sign-On identity provider and keeps all design safe and secure. Users can manage access control to the projects and provides notifications when anyone logs in the system.
The platform enables the users to start a discussion right on the app and solve any problem that arises in real-time. Moreover, its desktop app allows any number of people to work on a single sketch file. Lastly, users can save their designs in that way they want.
#47 ADManager Plus
ADManager Plus is a platform that enables the IT administrators and technicians to manage AD easily through an active directory management and reporting solution. The platform allows the companies to avail user accounts in AD and offers file server permission management for access control. Moreover, it allows companies to create multiple security and distribution groups and helps them in managing user accounts in bulk.
Companies can clean up the inactive or disabled accounts and can change the group of users in their Active Directory (AD). Moreover, it reduces the administration workload by automating most of the tasks of the companies.
The platform has a role-based security delegation and access control feature to minimize errors and keep the directory safe. Users can easily manage both AD and Microsoft Exchange Server from a single console. Lastly, it allows users to generate and export reports on Active Directory infrastructure and its active users.
#48 JumpCloud
JumpCloud is a (DaaS) Directory-as-a-Service solution designed to an organization’s users to securely connect and manage their devices, files, and networks anytime, anywhere. With the help of this, you can get complete to your cloud and on-premise platforms such as Microsoft Office 365, G Suite, AWS, and Jira, etc.
It also allows you to connect with servers to share files and networks. There is also has a feature that helps you to simplify identity management as well as also enable organizations to control and manage multiple devices from a single console. Just like all the other similar solutions, it also comes with system management features to ensure that laptops and servers within the environment are under control through a complete set of security tools.
JumpCloud allows businesses to integrate it with their Wi-Fi and VPN solutions to make it more robust and secure. With its SAML 2.0 and Single Sign-On protocols, you can also be able to authorization and authentication for both web and on-premises solutions.
#49 Ping Identity
Ping Identity is a platform that offers privacy and consent management and allows businesses to earn customer trust and comply with privacy regulations. The solution provides security to the customers and the workforce when it comes to their identities. It is a complete solution for all kinds of identity security services.
The platform helps businesses in providing their customers with easy-to-use registration, which helps them in acquiring and retaining customers. Moreover, companies can deliver personalized multi-channel experiences to enhance their revenues whenever customers interact with them. Companies can allow customers to gain full insight into their data to help them in building trust.
Ping Identity enables businesses to gain security over the identity of their workforce to keep their businesses secure. Moreover, it allows companies to improve their security posture and allows them to increase business agility by outpacing their competitors by cloud and rapid integrations.
#50 Kisi
Kisi is a flexible, agile, and secure cloud access control system that allows you to do all the management tasks with ease with vibrant office culture and collaboration. Now, Kisi is one of the leading physical security system providers to many organizations around the globe. The software provides your team an option with the keyless entry system and is now making its mark via delivering end-to-end solutions. You can meet your compliance need with the audit-trails as CSV files in case if you need access control audit to track SOC2.
The software comes with multiple deployment options and integration to automate the security management process. There are various features to offer that are Bluetooth NFC mobile access, CRM or active directory management, lockdown feature, easy access sharing, access hardware management, and more to add. Kisi is dispensing 24/7 support, and you can manage access and authorize co-workers from everywhere. You can easily streamline provisioning via creating access groups and extend your security with open API.