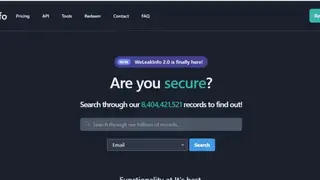
We Leak Info v2
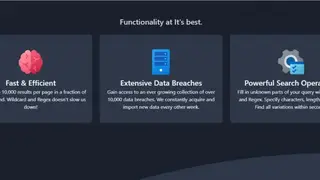
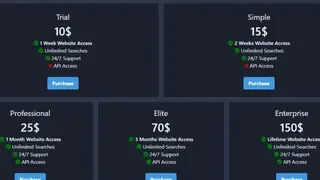
We Leak Info v2 is a new version of We Leak Info and helps users to know the condition of their emails, domains, and much more. The platform enables users to write the email address they want to check, and then they select the search option through which they want to check. It has a database of billions of records, and users can easily find through it what they are looking for.
The platform allows users to search the domain of any website or search the status of their IP address. Users can search email either by username or password. The service also allows users to search their phone status, whether it has been compromised through text or application.
We Leak Info v2 fetch up results in no time, and they can get details through the records. Moreover, its data is updated every week so that users can check new updates anytime. Lastly, it comes with powerful search operations that use the Wild card and Regex to fill unknown query parts.
We Leak Info v2 Alternatives
#1 Have I been pwned?
Have I been pwned? is a platform that enables users to know whether their personal data has been breached or not. The platform allows users to write their email addresses simply, and they can tell whether that email address has been compromised or not. Moreover, while searching the results, it keeps access to the user’s data and emails secure with the help of a unique password.
The platform allows users to get stats on the number of websites and email accounts whose data has been breached so far. Moreover, users can search any account from their collection to know which email account has been pwned. Users can also search the accounts which have been verified, and they can check accounts of different platforms to know their status.
Have I been pwned? Allows users to write their email in the notification sector through which they will be informed if their email is pwned. Lastly, users can perform a domain search to know about its condition and enter an email address to notify them.
#2 Inoitsu – Email Address Breach Analysis
Inoitsu – Email Address Breach Analysis is a platform that allows users to analyze their email to know whether it has been pwned or not. The platform enables users to write their email addresses in the provided search box and click on the submit button. It fetches the results in no time, and users can see what type of breach they had if there has been any. Moreover, users can also get a summary of their email addresses to know what kind of data is at risk and critical.
Furthermore, users can get updates on all the results gathered by different other platforms to know the condition of their addresses. It also takes all of the data from the service named as have I been pwned? Inoitsu – Email Address Breach Analysis enables users to get security tips and guidelines, and they can check the identity theft sites to know more about them. Lastly, it also helps them know about the fraud and theft detection of users’ data.
#3 LeakCorp
LeakCorp is one of the biggest platforms present to help users know whether their account has been breached or not. The platform enables users to access a database of billions of records through which they can find the account or domain they are searching for.
The platform has a simple interface through which users can search through the username or email address to know about their account status. The platform takes just milliseconds to respond to users with results, and they can see the condition of their account. If their account is included in the list, this means it has been breached; otherwise, they are lucky.
LeakCorp allows users to select the search type they want, such as they want to search for the email address, domain name, or username, and it will display results accordingly. However, users will have to buy it as it does not come with a free version or free trial to use this platform. Lastly, users can also search for the status of IP addresses.
#4 Spybot Identity Monitor
Spybot Identity Monitor is a flexible threat detecting software that provides you tools to check whether your information is in the hand of the hacker or not. The platform functioned on advanced technology that keeps you notified about the leakage of your data and information. Once you know your data is leaked, then you can instantly change your password.
The software has an easy installation setup and is simple to use with an elegant interface, and all you need to provide your email address, and you can see all details of the breach of your data. You can add accounts as many you want and get information about all your emails. Spybot identity Monitor is permitting a blazing service that provides you an overview of breaches and known sources for the set of an account.
#5 Snusbase
Snusbase is a legit data search engine that allows you to stay on top with the latest database breaches. The platform provides online security and information about the indexes that have been leaked from your website. Snubase allows users to search for emails, passwords, hashes, and usernames, to get access to the hacked information.
You can join all the major organizations and law enforcement using Snubase and can take proactive action from account takeovers. Snusbase results are always cleartext, and uncensored, and paying members can access everything included in the data breach. It is making the fraud and theft investigation easier by finding the criminal behind the screens. You can add Snubase to your external security suite with the developer API and gets out of the data-leak problem.
#6 LeakCheck
LeakCheck is a trusted platform that allows you to save the digital identity of people and organizations. The platform enables you to save credentials with API access for developers on any subscription. LeakCheck comes with the instant search results of your queries and facilitates you with the extensive databases that prevent you from searching for the data on the internet.
You can get new entries notification with vulnerable information, and you can load thousands of lines and get the result of each line. LeakCheck allows you to search by username, domain, password, hash, or keyword. The platform provides you with an advanced service that protects your data for about two years, and global organizations professionally benefit from Leackcheck.
#7 DeHashed
DeHashed is an advanced anti-fraud and Security tool that allows you to retrieve data from the hacked databases. The platform enables you to find your data where it is leaked and can be misused by hackers. DeHased has a straightforward and simple interface, and you have to adopt an easy procedure for finding your information.
The web-based software permits you to search for anything like username, email, passwords, address, or phone number. After the search, you should agree with the privacy policy to get to your data. DeHashed is using state-of-the-art technology; this means anything cannot go outside unless it is encrypted. The features that make DeHashed sumptuous are a fast search engine, high customer satisfaction, seamlessly working with the law of enforcement, breach analytics, live support to run any issue, and more to follow.
#8 NuclearLeaks
NuclearLeaks is a sophisticated platform that offers a vast amount of collection of publicly available website databases. The web-based software is facilitating security researchers and journalists to get access to the latest data and information that got leaked. NuclearLeaks is designed to acknowledge you about the database breaches via providing information about the data that has been leaked.
The platform comes with an advanced approach to save your data from any misuse and keep it safe and secure via maintaining your privacy on the internet. You can search either with username, email, phone, password, or address to find the secreted data. NuclearLeaks provides information about the total entries, hashing algorithms, categories, and dump date.
#9 MyPwd
MyPwd is an intelligent platfrom that facilitates you to find the email and password that have been leaked. The platform embraces a functional approach to take proactive action whenever your website, passwords, or usernames get hacked. MyPwd has a record of over nine billion leaked data, and you do not need to take any headache if you are the victim of data leakage.
The platform is doing a splendid job dealing with cybercriminals involved in various crimes such as bank scams, alteration of personal data, offenses committed in chat applications, and more. MyPwd ensues with the exceptional Artificial Intelligence that allows you to scan both deep and dark web comfortably.
The software continually looks for evidence for databases, credit card sales, illegal services, and attack planning with a comprehensive search engine. MyPwd empowers you to make better decisions when your data gets leaked and make changes through which your secreted data is always available. Moreover, the reliable alert system will notify you whenever new leakage is verified against your email so that you can make particular alterations.
#10 Databases.today
Databases.today is a flexible and reputable search engine that allows you to access the latest data basses and makes sure to stay safe online. The software is providing you with the cleartext results, and members can access names, addresses, add many more things included in the data breach. The software facilitates major organizations and law enforcement and allows you to take proactive actions against account takeovers.
The software comes with the proper fraud investigation procedure that is the primary concern in a small or large organization, and now finding a criminal is comfortable with advanced databases. The platform indexes the information from the website that is hacked or their databases got leaked and allowed the user to get their names, emails, usernames, phones, and even passwords that permit them to find the correct information if anything leaked. After a search, the data will display from the hacked site and provided to the user so they can update it and keep it out of the hands of the hackers.
#11 FireFox Monitor
FireFox Monitor is a useful and lean security tool that informs you when your used email got a leak. The platform is adopting a conventional approach to rectify the risk if your data is at risk or not, and if your information surfaces in a new data breach, the system directly notifies you. If you want breach notification, then you have must sign in for the alerts that include all reports on past breaches, including sensitive breaches.
The software has an intuitive interface and has a straightforward procedure to start the prosecution—all you need to put the email right in the search box and go for check breaches. After if your database is leaked, the system will provide your details. FireFox offers you ways for how you can save your data from criminals with conditional decisions.
#12 Leaksify
Leaksify is a platform that enables users to know whether their account has been compromised or not. The platform is one of the best and most authentic places for users to find out whether the email address, website, username, or any other account associated with those email addresses or usernames has been hacked. Users can enter their email address in the search bar to check whether their email address has been compromised or not.
Users can also enter the website or the username they use on different login platforms, and Leaksify will deliver the result of whether their account has been breached or not. Moreover, it provides that information that has been breached. Leaksify search every account against multiple data breach records and even informs users if their password or sensitive data has been breached or not. Lastly, if no data has been taken from the account, it displays it with no data written in red color.
#13 GhostProject.fr
GhostProject.fr is a platform that contains the database for the users about their accounts from whom data has been leaked. The platform comes with a simple interface that allows users to place their email address on the search box given and click search to find whether their data has leaked or not.
The platform allows users to view the compilation of recent 1.4 billion password breaches, and users can search for them with the help of email and username. Moreover, it tells users how they can protect their accounts and can keep their passwords safe. Lastly, users can donate to the platform either through Bitcoin or Dogecoin.
#14 LEAKED.SITE
LEAKED.SITE is a platform that offers free hacker tools that allow users to hack data anywhere and to keep their data safe at another end. The platform offers a database of tools that help users in keeping their data safe and secure. Users can search for the products which they are looking for through the search box, or they can directly go to the category which they need.
LEAKED.SITE offers tools such as Skype Resolver or Discord Resolver to allow users to know how they solve their hacking issues and keep their data safe. Moreover, it allows users to use its free and paid API services to integrate their system with its apps.
LEAKED.SITE allows users to check their GeoIP status and to know whether it is safe or not. Lastly, it allows users to scan their system and software to know if there is any virus, and it offers a free stress test to users to let them check whether their website is downable or not.
#15 LeakBase
LeakBase is a web-based new automated data forensic service data that allows you to check hacked data lookups from the data. The platform is providing you ways to get more aware of the data breaches and how to protect your information to get it out of the hands of the hacker.
Leakbase is easy to use the platform and has an intuitive web-based interface, and you must follow an easy procedure for checking your information is leaked or not. Leakbase comes with a server that allows users to search queries on different data basses and has a vast collection of databases.
#16 Hacksy
Hacksy is a platform that allows users to know whether their data has been leaked or not. It works as a security bot and allows users to make recommendations to users and helps them to make their data safe through better passwords. The platform acts as a security service and allows users to chat with the service for their security issues such as password strength, etc.
The platform offers such passwords that take a hundred years to crack to keep users’ data secured. Moreover, it enables users to know whether anyone has accessed their email or not.
Users just have to put their email address in the Hacksy platform, and it will tell them whether the data has leaked from it or not. Moreover, it also offers uncrackable social media accounts to keep everything secure. Lastly, it offers users secure browsing, phishing exercises, DDoS protection, and data protection.
#17 SkidBase
SkidBase is an online hacked data lookup service that enables you to find information about the leaked data courtesy of having a big database. With this online service, you can search our database of million records for free. One admirable thing about this site is that it provides you a comprehensive identify reports, and you can obtain some extra information from it.
The search results include information such as name, address, email address, and phone number. This platform is beneficial in protecting your social media accounts like Twitter, Xbox, and Instagram from hacking. No hassle is there; just all you need to sign up with an account and find out any leaked information. The searches that you will make are anonymous, and you will be able to see the accurate information transparently depending on your search criteria.
#18 Logaway
Logaway Logaway is an all-in-one online password manager, allows you to easily save and access to your any password-protected website. You can save multiple websites to include their usernames, passwords, or websites with all their sub-pages. You can sign up with Facebook or Twitter to make the process even faster. After that, you will be asked to make a master password for an account. It provides you a reliable way to access messenger for various social media platforms, including Facebook, Twitter, Yahoo, and more.
With Logaway, you can also have multiple accounts for the same site, which will help organize everything. This utility provides you with a customizable homepage, and there are icons that you will add for the sites that you want to visit. And whenever you are longing just all, you need to click the icon of the site, and you will be logged in automatically. For both your logaway password and your master password, you can have different types of choices. And to make sure your password is secure, Logaway will encrypt it using a unique algorithm.
#19 LeakedSource
LeakedSource is an online website that is created for dedicated professionals with digital security and privacy in mind. This useful utility provides you with the most comprehensive leaks database on the web. As you browse the site, you will be alerted to updates to the database. The leaked data is constantly updated and provided to the customers in the form of downloadable applications.
After extensive research and analysis, they were able to identify more than thousands of different leaks that are publicly available on various security-related. The search functionality in LeakedSource allows you to find your leaked passwords without any hassle at all. You can just input part of the email or domain and find out whether your email, domain, the password has been leaked before. LeakedSource will then provide you with the original source of your leaks.
#20 RogueRemover
RogueRemover is an intelligent tool that is the way to go for you in getting rid of any different rogue antivirus, antispyware, and various hard drive cleaning utilities. This software is the way to go for you, providing rich in-class support in finding the leaked data from your computer. The software is mostly emphasis the removal of the rogue application that has no usage and eating up your system resources all the time.
This extravagant utility provides real-time protection to your data against malicious sites with the help of a host file. RogueRemover software seems to be a leading source that provides real-time authentication to your device, and you will have detailed information on how your information has been leaked through your system.
#21 Leakwatch
Leakwatch is a flexible and command-line platform and Java API that allows you to monitor your data leaks from Java programs. The platform is free and easy to use and prevents your information from getting out during internet activities. Leakwatch is adopting a proactive Cybersecurity approach that permits you to detect exposed information via scanning. The platform comes with a collaborative team dedicated to assisting with flexible knowledge, and there is nothing to install. You can deal with data leakage with one centralized platform.
The platform provides you with quick information about the data leaks to take sudden actions. Leakwatch is surfacing qualified alerts with low false positives and actionable insight that give a clear understanding of the risks and choose the right steps to mitigate and do the best practice to keep your information out of the hands of hackers. You do not need any skill and technical knowledge with understandable insights and metrics. You can soundly build a data leak management roadmap with guidelines from techs to executives.
#22 We Leak Info
We Leak Info is a platform that offers data breach services to its users. The platform enables users to have access to more than eight billion records, and the database is updated on regular basis. Moreover, the data is never censored, which means visitors will get complete data anytime without deletion. The service offers a fast way to get things and data, and users can integrate the service into their system for quick access and use.
Moreover, users can use the public API through which they can see what kind of information it is taking and from where it is bringing that information. It enables users to search for the username, email, password, IP address, phone number, domain, etc., anything. We Leak Info allows users to perform wildcard and regex queries without ant performance degrade, and they can get all kinds of information through it.
#23 Forefront Threat Management Gateway
Forefront is one of the alluring threat management gateway designed for your windows system. This utility runs on the server of your windows and works via reviewing all traffic passing through it. The software is leveraging users with routing remote access features, including a VPN server, network address translation server, an internet gateway, and more to add. The system comes with advanced web caching, allowing you to cache frequently accessed web content, which is valuable for users to have faster access right from the local network cache.
Forefront Threat Management Gateway is providing rich security and privacy protection with its extravagant firewall system having the capability to inspect network traffic. It is also beneficial in filtering or sorting out malware and transparently getting detailed information about the attempts that are creating security vulnerabilities. The other rich features about this software are: layer protection, content filtering, stateful filtering, and anti-malware protection, improved network performance, and more to add.